In today’s world, we need to be constantly on the lookout for cyber-attacks coming from all sources of information. One of these sources is email. Mimecast provides protection against attacks coming in via email, however sometimes human interaction is required.
There are many reasons why an email may be held by the Mimecast system for review. Below are the most common reasons:
No email security will be able to route emails appropriately 100% of the time. The attacker’s strategies are constantly changing and as such we must always be on our toes for emails that may make it through and for emails that are held in quarantine.
Below are the different ways to manage emails in Mimecast. You can use one or all these methods depending on how your organization is configured. Keep in mind that even if you allow an email through the system, it may get caught in a different filter beyond that. Occasionally, additional configuration may be necessary to truly allow an email through the filter. Contact Method Technologies if this is the case and we can get to the bottom of why an email is being blocked.
The Postmaster Digest is the easiest method as it is a list of held emails that are in your “Personal On Hold” since the last time a digest was sent. Mimecast will send you a digest via email a few times per day. This digest will contain a list of all messages recently caught as spam. Typically, the sender will be “Postmaster” and the email looks like the below screenshot.
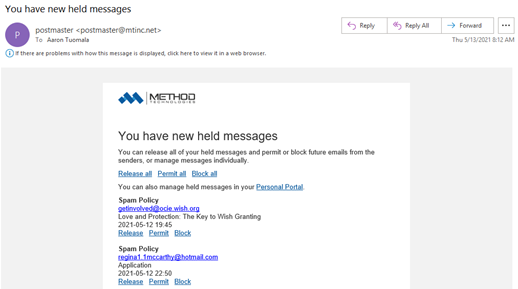
You can quickly scroll through the digest and act on any emails held by clicking the link below each message. Below are the three options available. In general, you would Permit/Release any messages that you need and ignore the rest. You do not need to act on every message.
If there are no emails you need to act on, you simply delete the digest and move on with your day. This works well for most people with the caveat that you will not be able to check this live as the digests only get sent every few hours. Keep in mind, that you ONLY need to select an option if you want to Release or Permit an email. In our opinion, using the Block selection is an effort in futility for most people as spam typically comes from different senders each time. If it is from a reputable source, we recommend unsubscribing instead of blocking in this method.
It is very important to note that the spam digest does not contain messages listed in the previous digest. This means that if you receive 3 digests per day (this is the default setting), you need to check all 3 to ensure you are not missing any messages. You will not receive a digest if no messages were caught as spam. As a final note, these digests only list spam items that are deemed questionable. There are many messages that are fully rejected at the gateway that will not be listed here. In these cases, the sender receives a bounce-back indicating that the message was not delivered. If a message is in the digest, the sender has not received a bounce-back.
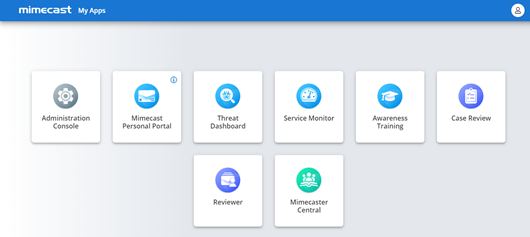
The Mimecast Personal Portal is probably the most used method of managing held email as it does not require the installation of any software and you can view held emails live as they come in. You can access the Mimecast Personal Portal by navigating in any browser to https://login.mimecast.com and entering your email address and password. This should be the same as your Microsoft 365 credentials.

Once signed in you will be provided a list of available apps you have access to. Select the “Mimecast Personal Portal” app.
You will then be redirected to the portal. It should look something like the below screenshot:
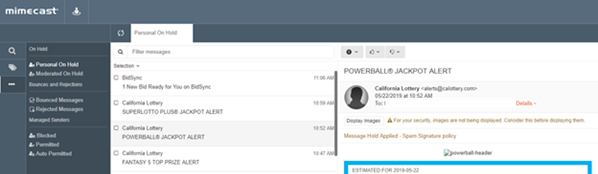
Once logged in, you can view your actively held emails as well as take action on any emails held. The default folder is “Personal On Hold”. The options available in this method are the same as the Digest, however you have additional options available to release or block not only for a specific email address, but also for the entire email domain. You must be very careful when doing this as permitting or blocking an entire domain could have unintended results. For example, if you block the entire domain of @gmail.com nobody with a Gmail email address will ever be able to email you. We recommend sticking with the individual address options instead.
You can release individual items by selecting the message and using the thumbs up or down icon above the message content. These actions are specific only to your user account, they do not whitelist them for other employees.
In the portal, you can also manage your existing Blocked and Permitted lists. If you inadvertently act on an address and later want to change that, you can use this portal to make that adjustment.
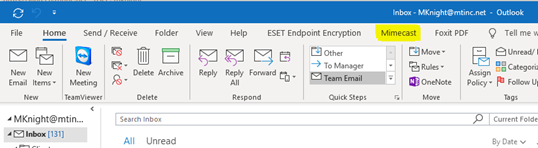
The Mimecast Outlook Plugin is our favorite method of managing held email as it is integrated directly within the Outlook application on your computer. To access the plugin, you simply click on the Mimecast tab and from there you have options that are very similar to the Mimecast Personal Portal above. This is, in our opinion, the most convenient way to manage held emails.
You must have the Outlook plugin installed for this to work. Please contact Method Technologies if you wish to have the plugin installed.
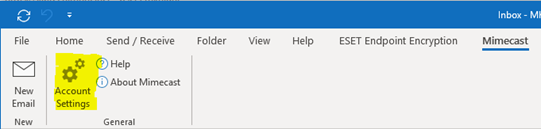
Once installed, open Outlook and click on the Mimecast tab at the top.
Click on Account Settings to log into the plugin.
A new window will open. You will be prompted for Cloud or sometimes Domain Authentication options. Your authentication type may vary, some customers are configured with Cloud Authentication and others with Domain Authentication. We suggest using the Personal Portal instructions above to verify your login prior to configuring the Mimecast Outlook Plugin. This guide will assume you are using Domain Authentication. Under the Domain Authentication section, click the Authenticate button.
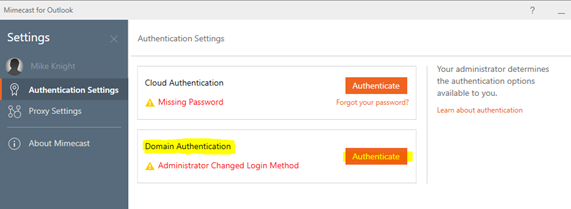
Your email address should already be populated, if it is not then enter your email as well as your Microsoft 365 password and click Submit Password.
Once completed, the status of Domain Authentication should show Active and you can close the window. At this point the Mimecast tab in Outlook will be populated with several options:
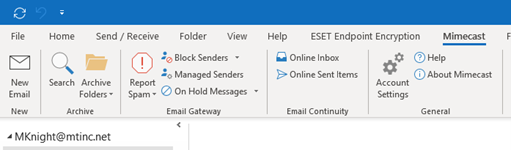
The most used feature of this plugin is the On Hold Messages button – This option opens a new window that shows you messages in your Held queue. These will be listed in the digest that is sent every few hours, but viewing it here allows you to release them without waiting for the digest. This will also show messages from previous digests, up to 30 days. Other important functions are listed below:
The Mimecast mobile app is great for checking your held emails on the go. To access the app simply download it from the Google Play or Apple app store on your mobile device. Once logged in, you have options that are very similar to the Mimecast Personal Portal above, but on your phone. This is extremely helpful when you need to get that occasional password reset email or two factor code that may be caught in your help messages and you are not at a computer.
Targeted Threat Protection protects users from malicious links sent in emails and attachments. In general, this does not represent a change in workflow for any staff unless an issue arises.
When a user clicks a link in an email, they will first be redirected to Mimecast’s website which will process the link and then forward the request if it is legitimate. If for some reason the link was not legitimate, then the user will see a warning like this:
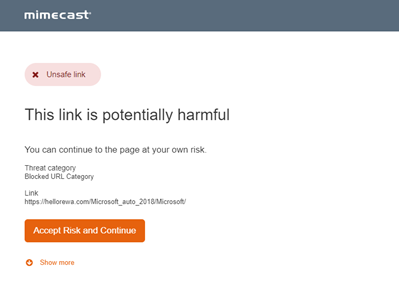
If the user chooses to continue to the site, then a notification will be sent (either to Method, or to a designated contact at your company) indicating that the user performed this action. It is rarely necessary to bypass the warning, however the occasional false positive is detected. If you routinely receive false positives from a specific source, contact us and we can whitelist the URL.
Note that the URL scanning feature does add a small delay (a few seconds) to loading web pages from email links. This is expected and is part of the security measure. As always if you have any questions feel free to contact Method Technologies for assistance.
Occasionally you may get an email from Mimecast about a specific message that was caught in a more severe filter, such as Impersonation Protection. These emails are typically Phishing attempts and generally require oversight on the decision made due to the potential impact it may have on the organization. You do have the ability to release these types of emails from your held emails, however the email notification does not provide a way to do that directly. You must login to one of the portals above to take the action. If there is ever a doubt on the legitimacy of an email, please contact Method Technologies for assistance.
Impersonation protection protects against “Spear phishing” or “Whaling” type attacks. These attacks do not use a harmful attachment or website, but instead rely purely on social engineering. In general, a malicious person will pretend to be another member of your company and ask for a wire transfer, credit card number, credentials, etc. They will even go as far to register a new domain name similar to your company’s (for example if your domain is company.com, they may register cornpany.com or company.co).
Impersonation Protection looks for various parts of the email to determine if it thinks it is fraudulent. These usually include:
If two or more of the above criteria are met, then you and the administrator will receive a message like this:
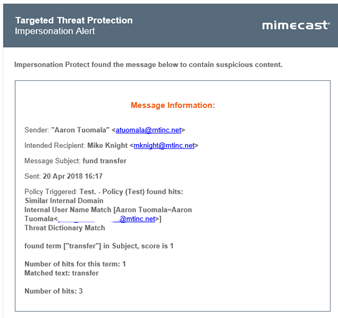
In most cases, you do not need to do anything. If this is a false positive, you have the ability to login into Mimecast via one of the methods covered previously to release the message. As always, if you are unsure, you can contact Method Technologies to assist and to even whitelist the address if needed. If you are receiving these alerts constantly, you should speak to Method Technologies or your supervisor.